Affianced!
Michael & Molly October 25th 2024

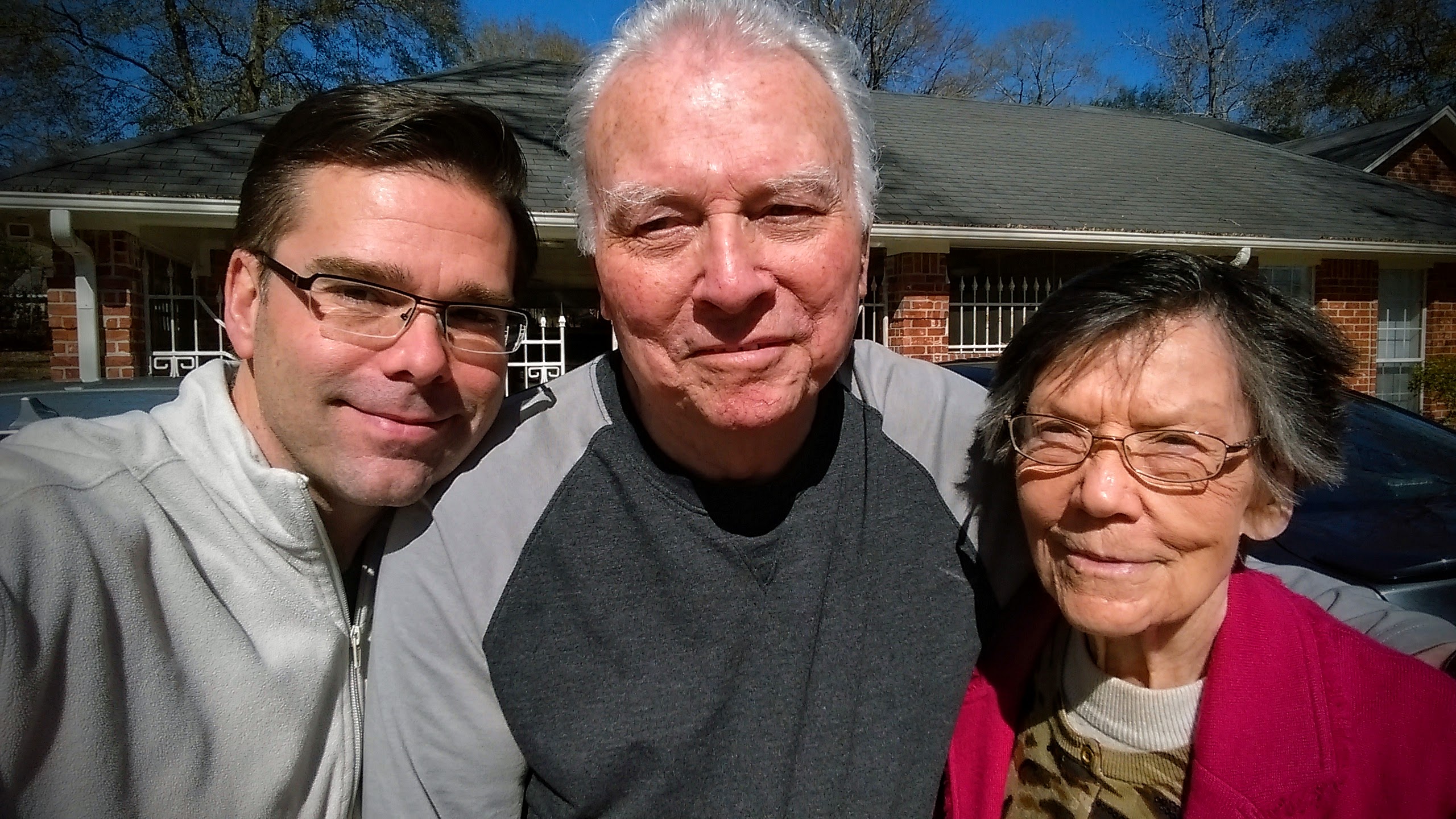
Viola Louise Smith Tillery Turner
January 27 1924 – December 5 2022

Randell “Papaw” Turner
April 28 1921 – September 28 2018
Mr. Randell Turner, 97, of Jasper, Texas passed away peacefully on Friday, September 28, 2018. Randell was born in Lexington, Texas to Archie Wright Turner and Sealy Ann (Howry) Turner on April 28,1921.
He graduated from Port Neches High School in 1938 and began to work as a ship-fitter with Brown Ship Building and Consolidated Steel Corp. Randell served in World War II in the 3rd Army and was in involved in battles at Ardennes and Rhineland. He then operated as an attaché during the Nuremberg trials. In the 1980’s, he retired from A & M Sheet Metal. Randell was a long-standing member of the Shriner’s and the American Legion.
He leaves behind his wife, Viola Louise; nephews Doug Turner and Randy Turner; and his grandchildren Michael, Jeanette, Mikey and Bradley Hanson
Our Papaw will missed dearly and remembered fondly. He was kind, gentle and wise and exceedingly generous. He made a lasting impact on all of us.














![[FSF Associate Member]](http://www.hx4.com/wp-content/uploads/2015/03/FSF-52816.png)